How Smart Contracts Are Maintained After Deployment
Best Practices for Monitoring, Upgrading, and Securing Deployed Smart Contracts
Smart contracts are often described as “immutable,” a term that suggests permanence and finality. Once deployed to a blockchain, the contract code cannot be changed in the traditional sense. While this immutability is fundamental to trust and transparency, it does not mean smart contracts are abandoned after deployment. In practice, maintaining smart contracts is an ongoing, carefully structured process that balances decentralization with adaptability, security, and long-term reliability.
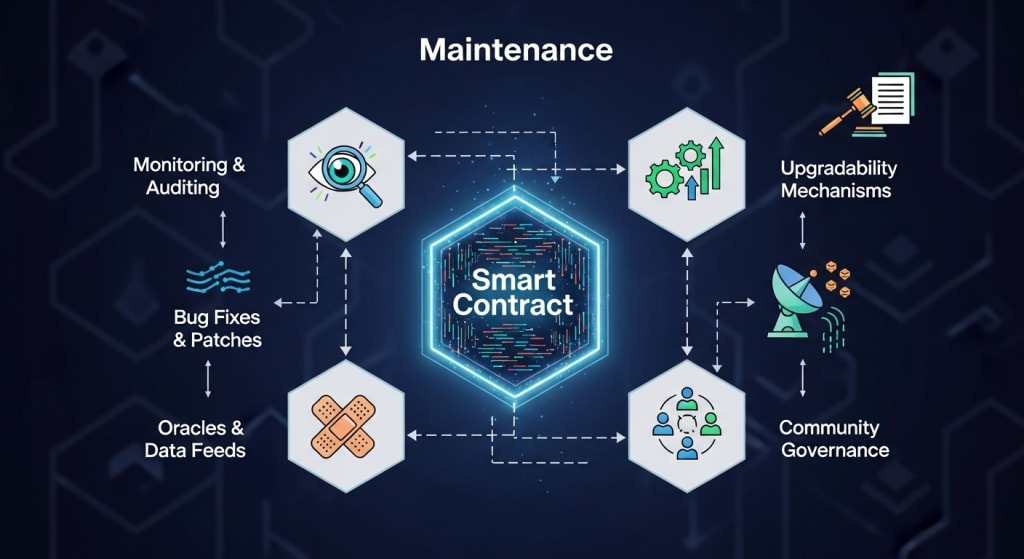
Post-deployment maintenance determines whether a decentralized application (dApp) remains secure, usable, and economically viable. From monitoring on-chain behavior to managing upgrades, responding to vulnerabilities, and evolving governance rules, maintenance is where smart contracts either mature into robust systems or become liabilities. This article explores how smart contracts are maintained after deployment, focusing on real-world practices, architectural patterns, and lessons learned from major blockchain ecosystems.
The Reality of Immutability and Why Maintenance Still Matters
Immutability ensures that no single party can secretly alter contract logic after deployment. This property underpins trustless execution but also introduces risk: bugs, economic exploits, or regulatory changes cannot be patched with a simple code update. High-profile incidents such as early decentralized finance (DeFi) exploits revealed that “set and forget” contracts can lock in vulnerabilities just as permanently as they lock in rules.
Maintenance, therefore, does not mean editing deployed code directly. Instead, it involves designing systems that anticipate change, continuously monitoring contract behavior, and implementing controlled mechanisms for adaptation. Modern blockchain development treats deployment as the beginning of a lifecycle rather than its end.
Monitoring Live Smart Contracts in Production
Once a smart contract is live, visibility becomes critical. Monitoring tools track contract interactions, transaction volumes, gas usage, and abnormal patterns that could signal exploits or misuse. On public blockchains, all activity is transparent, but raw data must be interpreted correctly to be actionable.
Maintenance teams monitor metrics such as:
Sudden spikes in function calls that may indicate automated attacks
Gas consumption anomalies that could reflect inefficient logic or malicious loops
Token flow irregularities suggesting economic manipulation
For example, many DeFi protocols implement real-time alerting systems that notify developers and governance participants when critical thresholds are crossed. In several documented cases, early detection of abnormal transaction behavior allowed communities to pause frontend access or trigger emergency governance actions before funds were fully drained.
Effective monitoring transforms the blockchain’s transparency into operational intelligence, allowing stakeholders to respond quickly even though the underlying code remains immutable.
Upgradeability Patterns: Designing for Change Without Breaking Trust
One of the most important maintenance strategies is upgradeable contract architecture. Instead of deploying a single, monolithic contract, developers separate logic from storage. The most common approach is the proxy pattern, where users interact with a stable proxy contract that delegates execution to an upgradeable implementation contract.
This design allows:
Bug fixes and feature additions without changing contract addresses
Preservation of user balances and state data
Transparent, auditable upgrade processes
However, upgradeability introduces governance and trust considerations. Who controls upgrades? How are changes approved? Poorly governed upgrades can undermine decentralization by concentrating power in a small group of administrators. To mitigate this, many protocols require multi-signature approvals or on-chain governance votes before upgrades are executed.
In practice, upgradeable contracts represent a compromise: they preserve immutability at the interface level while allowing controlled evolution beneath the surface.
Governance as a Core Maintenance Mechanism
Smart contract maintenance increasingly relies on decentralized governance. Instead of relying solely on development teams, protocols distribute decision-making authority to token holders or elected delegates. Governance proposals can include parameter changes, contract upgrades, treasury allocations, or emergency responses to threats.
This governance-driven maintenance model offers several advantages:
Decisions are transparent and publicly auditable
Responsibility is distributed rather than centralized
Economic incentives align users with long-term protocol health
Real-world examples show both strengths and weaknesses. Well-designed governance frameworks have successfully coordinated complex upgrades across millions of users. At the same time, low voter participation or governance capture by large token holders can slow responses or skew outcomes. Maintenance, therefore, depends not only on technical design but also on active community engagement.
Security Reviews After Deployment
Contrary to popular belief, audits do not end at deployment. Ongoing security assessments are a critical part of maintenance, especially as usage patterns evolve and new attack vectors emerge. Economic exploits, such as flash-loan attacks, often arise from interactions between multiple contracts rather than flaws in isolated code.
Post-deployment security practices include:
Continuous review of on-chain behavior against threat models
Periodic re-audits after major upgrades or integrations
Bug bounty programs that incentivize responsible disclosure
Data from leading bug bounty platforms shows that proactive reward programs can reduce exploit severity by encouraging white-hat researchers to report vulnerabilities before attackers exploit them. Maintenance, in this sense, becomes a collaborative effort between developers and the broader security community.
Handling Emergency Situations and Incident Response
No system is immune to failure. Mature smart contract maintenance plans include predefined emergency procedures. These may involve pause functions, rate limits, or circuit breakers that temporarily restrict functionality during abnormal conditions.
While pause mechanisms are controversial due to centralization concerns, real-world incidents demonstrate their value. In several major exploits, the ability to halt certain contract functions limited losses and bought time for governance decisions. The key is transparency: users must clearly understand under what conditions emergency controls can be used and who has the authority to activate them.
Effective incident response combines technical safeguards with clear communication. Prompt disclosure, post-mortem analysis, and compensation plans can preserve trust even after serious failures.
Interoperability and Dependency Management
Smart contracts rarely operate in isolation. They depend on external contracts, price oracles, bridges, and off-chain data providers. Maintenance must account for these dependencies, as changes or failures in one component can cascade across the system.
For example, oracle failures have historically caused incorrect pricing, triggering mass liquidations or arbitrage exploits. To reduce dependency risk, protocols often:
Use multiple data sources with aggregation logic
Implement fallback mechanisms
Monitor external contract upgrades that could affect integrations
As blockchain ecosystems become more interconnected, maintenance increasingly resembles systems engineering, where reliability depends on managing relationships between many moving parts.
Long-Term Evolution and Technical Debt
Over time, even well-designed smart contracts accumulate technical debt. Early architectural decisions may limit scalability, efficiency, or feature expansion. Maintenance involves making strategic decisions about when to upgrade incrementally and when to migrate users to entirely new contracts.
Some protocols choose staged migrations, deploying new versions alongside legacy contracts and incentivizing users to transition voluntarily. While complex, this approach avoids breaking compatibility and respects user autonomy. It also reflects a mature understanding that smart contract systems are living infrastructures, not static artifacts.
Organizations offering a smart contract development solution, a smart contract development firm, or a web3 smart contract development company often emphasize this lifecycle perspective, helping projects plan not just for launch, but for years of evolution.
Conclusion
Smart contracts promise automation, trust minimization, and transparency, but these benefits only endure through disciplined maintenance after deployment. Monitoring, upgradeability, governance, security, and incident response are not optional add-ons; they are core components of sustainable decentralized systems.The most successful blockchain projects treat deployment as a milestone, not a finish line. By anticipating change, designing for adaptability, and engaging their communities, they transform immutability from a constraint into a foundation for long-term trust. In an ecosystem where code governs value, how smart contracts are maintained ultimately determines whether they fulfill their revolutionary potential.
About the Creator
Dominic34
I specialize in helping blockchain startups and crypto projects launch, grow, and scale through strategic token development, decentralized fundraising guidance, and Web3-focused marketing.






Comments
There are no comments for this story
Be the first to respond and start the conversation.